SolarWinds Security Event Manager Workstation Edition SWE1000 (up to 1000 nodes) and SEM150 – 105602 – Annual Subscription
Includes
- Centralized log collection and normalization
- Automated threat detection and response
- Integrated compliance reporting tools
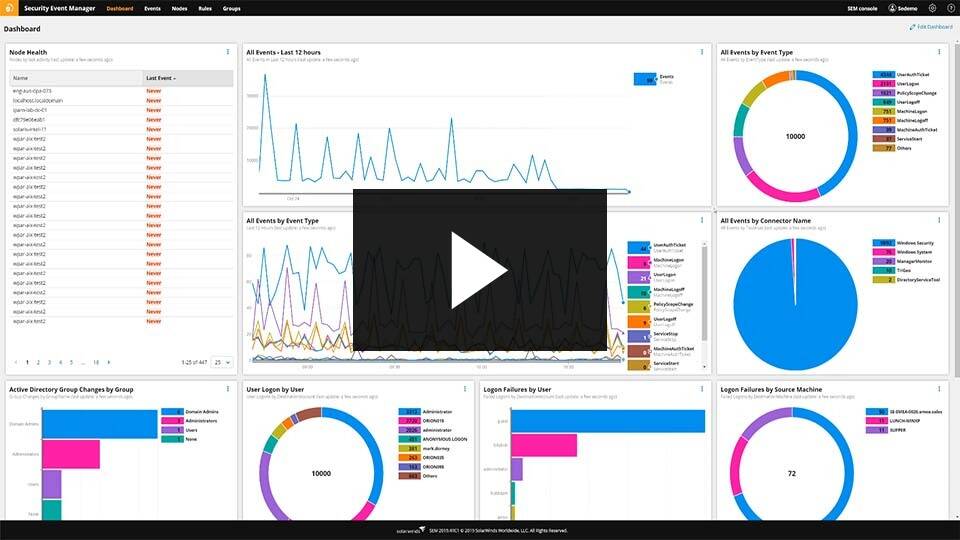
- Intuitive dashboard and user interface
- Built-in file integrity monitoring
- Simple and affordable licensing
For The Immediate delivery contact the sales team. Usually, Ship in 2-3 days, images are for illustration purposes only.
Call for Price
SolarWinds Security Event Manager Workstation Edition SWE1000 (up to 1000 nodes) and SEM150 – 105602 – Annual Subscription
- Centralized log collection and normalization
- Automated threat detection and response
- Integrated compliance reporting tools
- Intuitive dashboard and user interface
- Built-in file integrity monitoring
- Simple and affordable licensing
PN: 105602
Overview
Thousands of resource-constrained IT and security pros rely on SolarWinds® Security Event Manager (SEM) for affordable and efficient threat detection, automated incident analysis and response, and compliance reporting for their IT infrastructure. Our SIEM solution combines log management, threat detection, normalization and correlation, forwarding, reporting, file integrity monitoring, user activity monitoring, USB detection and prevention, threat intelligence, and active response in a virtual appliance that’s easy to deploy, manage, and use. We’ve designed our SIEM to provide the functionality you need without the complexity and cost of most other enterprise SIEM solutions.
SECURITY EVENT MANAGER AT A GLANCE
- Collects, consolidates, normalizes, and visualizes logs and events from firewalls, IDS/IPS devices and applications, switches, routers, servers, OS, and other applications
- Performs real-time correlation of machine data to identify threats and attack patterns
- Responds to suspicious activity automatically with Active Response, including blocking USB devices, killing malicious processes, logging off users, and more
- Eases compliance reporting and audits with out-of-the-box reports and filters for HIPAA, PCI DSS, SOX, ISO, DISA STIGs, FISMA, FERPA, NERC CIP, GLBA, and more
- Offers an intuitive interface and ample selection of out-of-the-box content, meaning you don’t need to be a security or compliance expert to get value from SolarWinds SEM
- Affordable, scalable licensing based on log-emitting sources, not log volume
Features
A SIEM solution without unnecessary complexity or cost.
Identify and respond to threats faster
Security Event Manager (SEM) will be another pair of eyes watching 24/7 for suspicious activity and responding in real time to reduce its impact.
See value quickly
Virtual appliance deployment, intuitive UI, and out-of-the-box content means you can start getting valuable data from your logs with minimal expertise and time.
Ease compliance reporting and audits
Minimize the time it takes to prepare and demonstrate compliance with audit proven reports and tools for HIPAA, PCI DSS, SOX, and more.
Get more data for less
Our licensing is based on the number of log-emitting sources, not log volume, so you won’t need to be selective about the logs you gather to keep costs down.
Detecting threats and demonstrating compliance doesn’t have to be complicated.
Do you find yourself asking…
Why does it take so long to find the log data I need?
Security Event Manager comes with hundreds of pre-built connectors to gather logs from various sources, parse their data, and put it into a common readable format, creating a central location for you and your team to easily investigate potential threats, prepare for audits, and store logs.
Security Event Manager includes features to quickly and easily narrow in on the logs you need, such as visualizations, out-of-the-box filters, and simple, responsive text-based searching for both live and historical events. With scheduled search, you can save, load, and schedule your most commonly used searches.
What can I do to be more aware of security threats?
Security Event Manager can act as your own SOC, alerting you to the most suspicious behaviors, and allowing you to focus more of your time and resources on other critical projects. SEM has hundreds of built in correlation rules to watch your network and piece together data from the various log sources to identify potential threats in real time. Not only will you have out-of-the-box correlation rules to help get you started, but the normalization of log data allows for an endless combination of rules to be created. Additionally, SEM has an integrated threat intelligence feed working to identify behaviors originating from known bad actors.
How can I make complex audit and compliance reporting easier?
SEM provides hundreds of out-of-the-box reports to help you demonstrate compliance for HIPAA, PCI DSS, SOX, ISO, DISA STIGs, FISMA, FERPA, NERC CIP, GLBA, GPG13, and more.
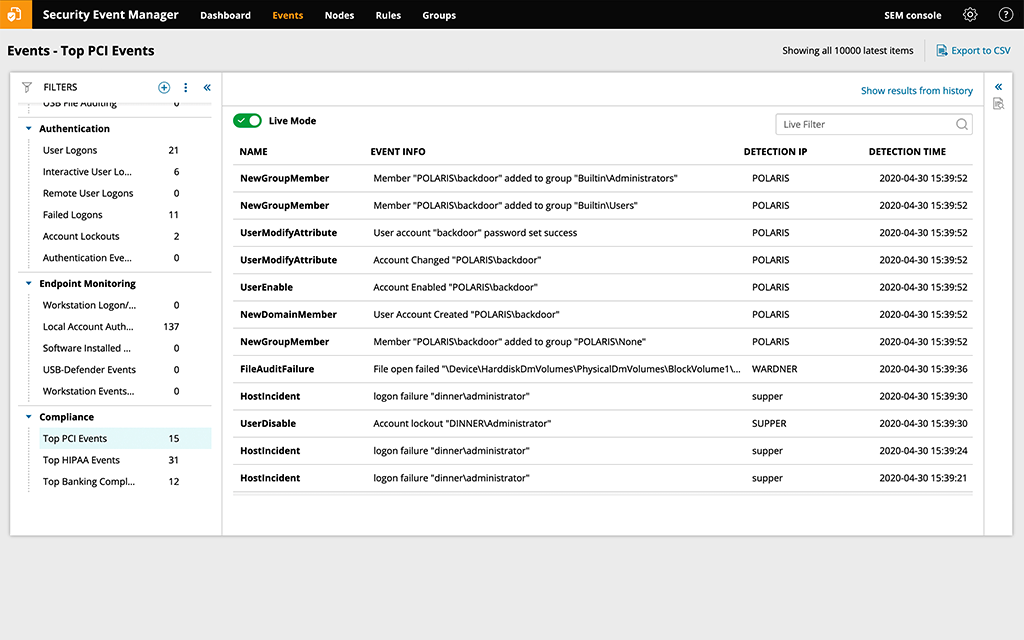
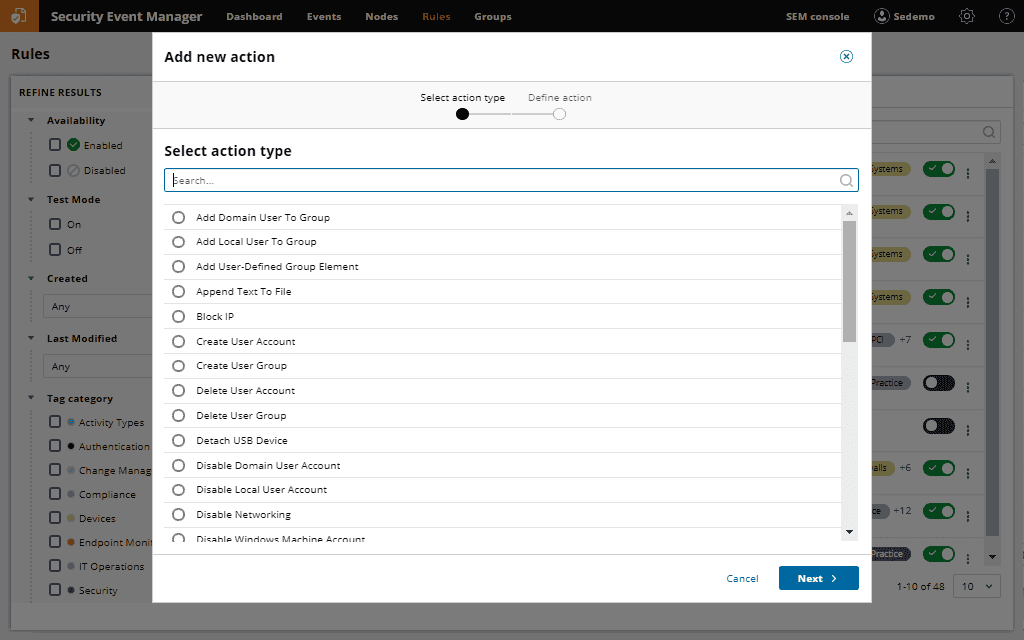
How can we respond to cyberthreats faster?
The cost of a data breach can be reduced by how quickly you identify the threat and start addressing it. With Security Event Manager, you can hasten your responses by automating them when certain correlation rules are triggered. Responses include block IPs, change privileges, disable accounts, block USB devices, kill applications, and more.
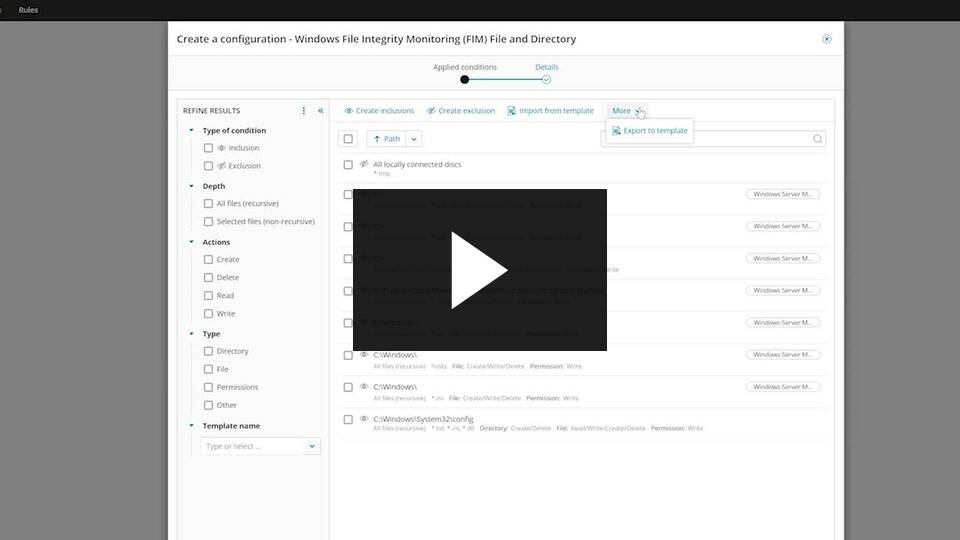
How can I track file changes, directory access, movement, and shares?
Modifications, deletions, and permission changes to files, folders, and registry settings could be the sign of a potential data breach. You can monitor and be alerted to suspicious or potentially malicious activity in sensitive files with Security Event Manager’s built-in File Integrity Monitoring (FIM) capabilities.
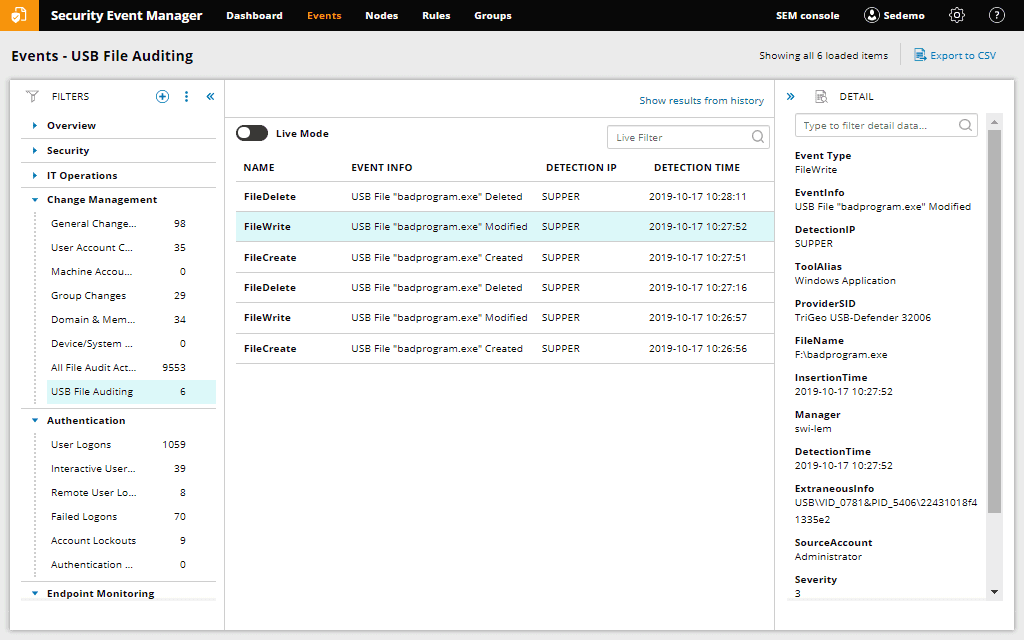
Can I reduce the risk of unmanaged flash drives on my network?
Unmanaged USB flash drives pose an ongoing risk to IT security. Security Event Manager is designed to provide valuable insight into file and USB activity with the built-in USB defender. USB defender helps enforce USB policies and will take automated response if an unmanaged USB is plugged into your network.
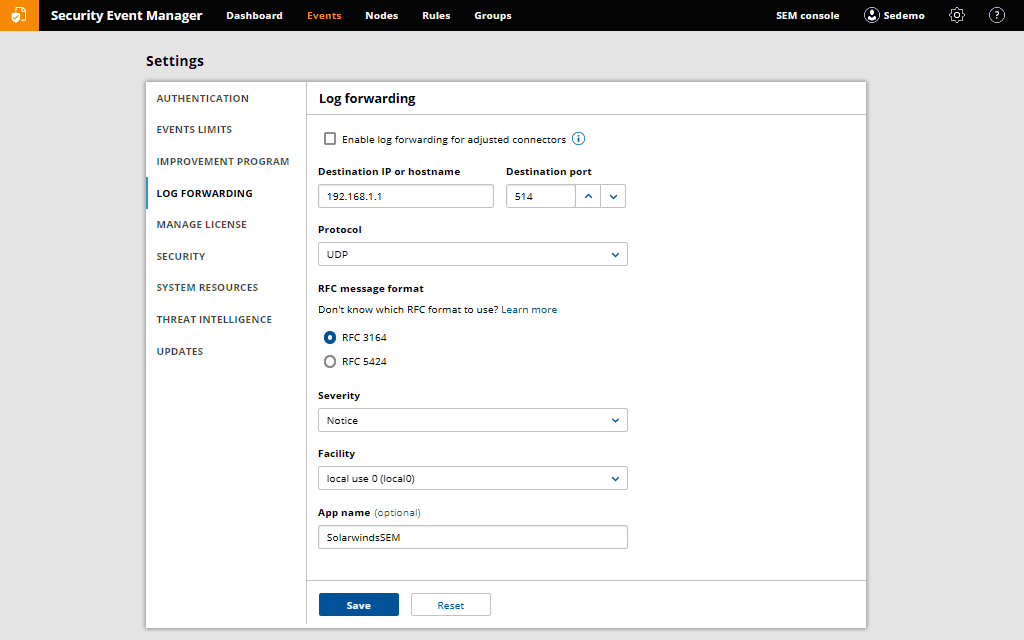
How do we get logs to the right people and places and still have a centralized repository?
Security Event Manager is designed to easily forward raw event log data with syslog protocols (RFC3164 and RFC 5244) to an external application for further use or analysis. Additionally, with one click, you can export your filtered or searched log data to CSV, making it incredibly fast and easy to share log data with other teams or vendors.
Published on lastbestprice.com
Datasheet







































Reviews
There are no reviews yet.